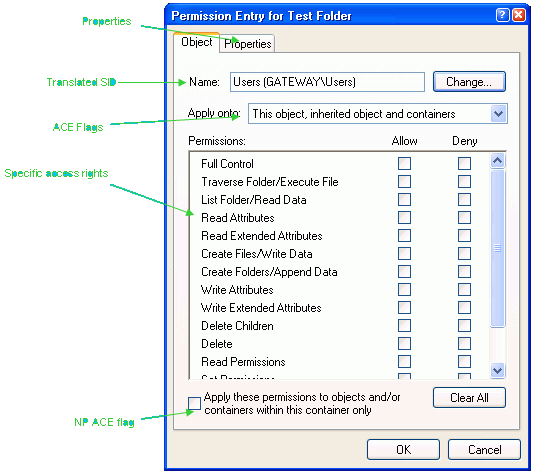
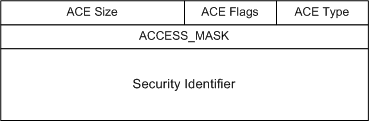
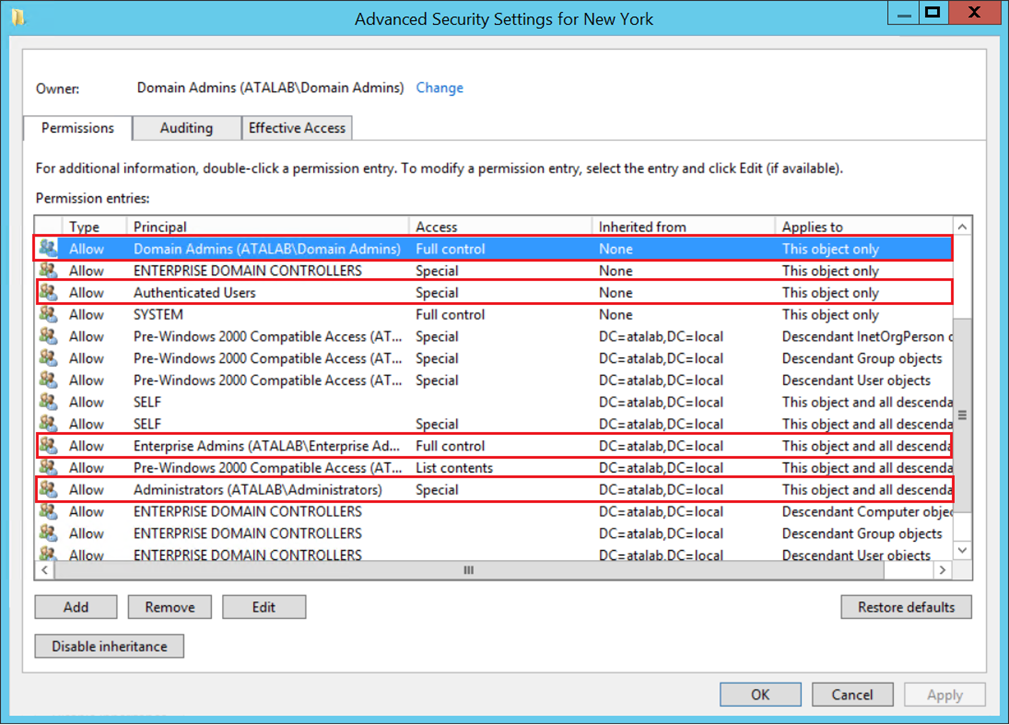
How to target and identify dangerous Access Control Entries in NT Security Descriptor-related deviances?

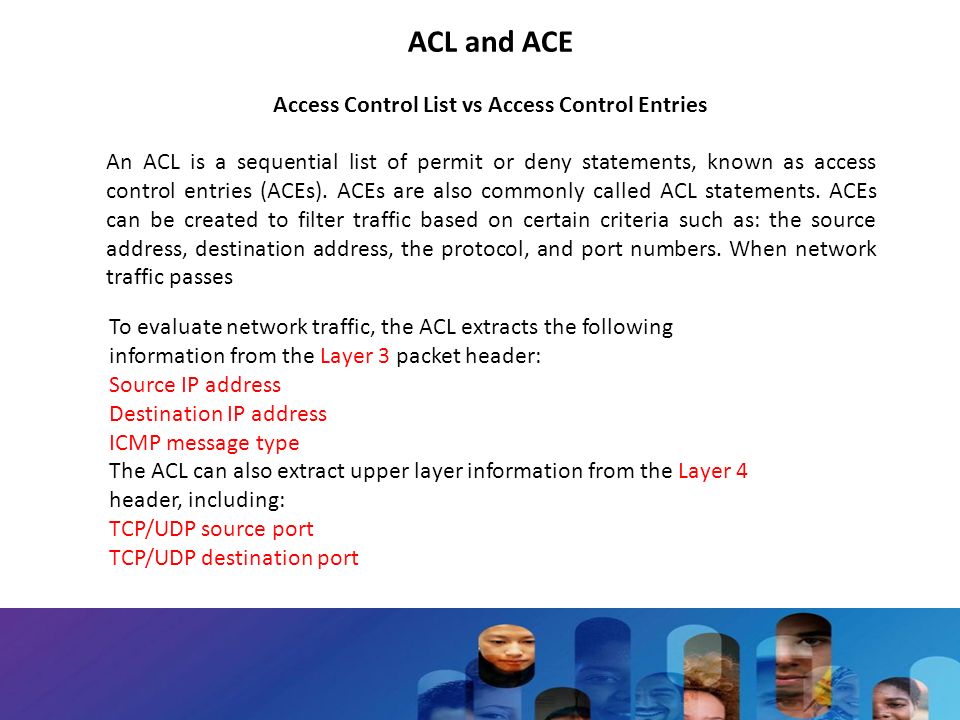
FileNet P8 Development tutorials: Access Control List(ACL) and Access Control Entry(ACE) (FileNet Content Engine)
GitHub - OTRF/Set-AuditRule: Useful access control entries (ACE) on system access control list (SACL) of securable objects to find potential adversarial activity